Lab4e: Managing access keys for IAM users
Access keys are long-term credentials for an IAM user or the AWS account root user. You can use access keys to sign programmatic requests to the AWS CLI or AWS API (directly or using the AWS SDK). For more information, see Signing AWS API requests.
Access keys consist of two parts: an access key ID (for example, AKIAIOSFODNN7EXAMPLE) and a secret access key (for example, wJalrXUtnFEMI/K7MDENG/bPxRfiCYEXAMPLEKEY). You must use both the access key ID and secret access key together to authenticate your requests.
When you create an access key pair, save the access key ID and secret access key in a secure location. The secret access key is available only at the time you create it. If you lose your secret access key, you must delete the access key and create a new one. For more details, see Resetting lost or forgotten passwords or access keys for AWS.
Important
Manage your access keys securely. Do not provide your access keys to unauthorized parties, even to help find your account identifiers. By doing this, you might give someone permanent access to your account.
The following topics detail management tasks associated with access keys.
Topics
- Permissions required to manage access keys
- Managing access keys (console)
- Managing access keys (AWS CLI)
- Managing access keys (AWS API)
- Updating access keys
- Securing access keys
- Auditing access keys
Permissions required to manage access keys
Note
iam:TagUser is an optional permission for adding and editing descriptions for the access key. For more information, see Tagging IAM users
To create access keys for your own IAM user, you must have the permissions from the following policy:
{
"Version": "2012-10-17",
"Statement": [
{
"Sid": "CreateOwnAccessKeys",
"Effect": "Allow",
"Action": [
"iam:CreateAccessKey",
"iam:GetUser",
"iam:ListAccessKeys",
"iam:TagUser"
],
"Resource": "arn:aws:iam::*:user/${aws:username}"
}
]
}To update access keys for your own IAM user, you must have the permissions from the following policy:
{
"Version": "2012-10-17",
"Statement": [
{
"Sid": "ManageOwnAccessKeys",
"Effect": "Allow",
"Action": [
"iam:CreateAccessKey",
"iam:DeleteAccessKey",
"iam:GetAccessKeyLastUsed",
"iam:GetUser",
"iam:ListAccessKeys",
"iam:UpdateAccessKey",
"iam:TagUser"
],
"Resource": "arn:aws:iam::*:user/${aws:username}"
}
]
}Managing access keys (console)
To create, modify, or delete your own access keys (console)
- Use your AWS account ID or account alias, your IAM user name, and your password to sign in to the IAM console.
Note
For your convenience, the AWS sign-in page uses a browser cookie to remember your IAM user name and account information. If you previously signed in as a different user, choose Sign in to a different account near the bottom of the page to return to the main sign-in page. From there, you can type your AWS account ID or account alias to be redirected to the IAM user sign-in page for your account.
To get your AWS account ID, contact your administrator.
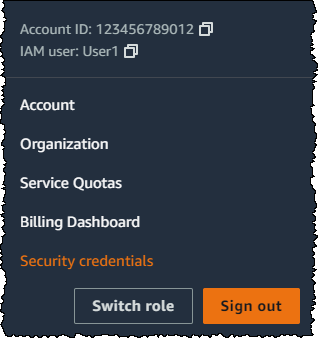
- In the navigation bar on the upper right, choose your user name, and then choose Security credentials.
Do one of the following:
To create an access key
- In the Access keys section, choose Create access key. If you already have two access keys, this button is deactivated and you must delete an access key before you can create a new one.
- On the Access key best practices & alternatives page, choose your use case to learn about additional options which can help you avoid creating a long-term access key. If you determine that your use case still requires an access key, choose Other and then choose Next.
- (Optional) Set a description tag value for the access key. This adds a tag key-value pair to your IAM user. This can help you identify and update access keys later. The tag key is set to the access key id. The tag value is set to the access key description that you specify. When you are finished, choose Create access key.
- On the Retrieve access keys page, choose either Show to reveal the value of your user’s secret access key, or Download .csv file. This is your only opportunity to save your secret access key. After you’ve saved your secret access key in a secure location, choose Done.
To deactivate an access key
- In the Access keys section find the key you want to deactivate, then choose Actions, then choose Deactivate. When prompted for confirmation, choose Deactivate. A deactivated access key still counts toward your limit of two access keys.
To activate an access key
- In the Access keys section, find the key to activate, then choose Actions, then choose Activate.
To delete an access key when you no longer need it
- In the Access keys section, find the key you want to delete, then choose Actions, then choose Delete. Follow the instructions in the dialog to first Deactivate and then confirm the deletion. We recommend that you verify that the access key is no longer in use before you permanently delete it.
To create, modify, or delete the access keys of another IAM user (console)
- Sign in to the AWS Management Console and open the IAM console at https://console.aws.amazon.com/iam/.
- In the navigation pane, choose Users.
- Choose the name of the user whose access keys you want to manage, and then choose the Security credentials tab.
- In the Access keys section, do any of the following:
- To create an access key, choose Create access key. If the button is deactivated, then you must delete one of the existing keys before you can create a new one. On the Access key best practices & alternatives page, review the best practices and alternatives. Choose your use case to learn about additional options which can help you avoid creating a long-term access key. If you determine that your use case still requires an access key, choose Other and then choose Next. On the Retrieve access key page, choose Show to reveal the value of your user’s secret access key. To save the access key ID and secret access key to a
.csvfile to a secure location on your computer, choose the Download .csv file button. When you create an access key for your user, that key pair is active by default, and your user can use the pair right away. - To deactivate an active access key, choose Actions, and then choose Deactivate.
- To activate an inactive access key, choose Actions, and then choose Activate.
- To delete your access key, choose Actions, and then choose Delete. Follow the instructions in the dialog to first Deactivate and then confirm the deletion. AWS recommends that before you do this, you first deactivate the key and test that it’s no longer in use. When you use the AWS Management Console, you must deactivate your key before deleting it.
- To create an access key, choose Create access key. If the button is deactivated, then you must delete one of the existing keys before you can create a new one. On the Access key best practices & alternatives page, review the best practices and alternatives. Choose your use case to learn about additional options which can help you avoid creating a long-term access key. If you determine that your use case still requires an access key, choose Other and then choose Next. On the Retrieve access key page, choose Show to reveal the value of your user’s secret access key. To save the access key ID and secret access key to a
To list the access keys for an IAM user (console)
- Sign in to the AWS Management Console and open the IAM console at https://console.aws.amazon.com/iam/.
- In the navigation pane, choose Users.
- Choose the name of the intended user, and then choose the Security credentials tab. In the Access keys section, you will see the user’s access keys and the status of each key displayed.
Note
Only the user’s access key ID is visible. The secret access key can only be retrieved when the key is created.
To list the access key IDs for multiple IAM users (console)
- Sign in to the AWS Management Console and open the IAM console at https://console.aws.amazon.com/iam/.
- In the navigation pane, choose Users.
- If necessary, add the Access key ID column to the users table by completing the following steps:
- Above the table on the far right, choose the settings icon (
).
- In Manage columns, select Access key ID.
- Choose Close to return to the list of users.
- Above the table on the far right, choose the settings icon (
- The Access key ID column shows each access key ID, followed by its state; for example, 23478207027842073230762374023 (Active) or 22093740239670237024843420327 (Inactive).
You can use this information to view and copy the access keys for users with one or two access keys. The column displays None for users with no access key.
Note
Only the user’s access key ID and status is visible. The secret access key can only be retrieved when the key is created.
To find which IAM user owns a specific access key (console)
- Sign in to the AWS Management Console and open the IAM console at https://console.aws.amazon.com/iam/.
- In the navigation pane, choose Users.
- In the search box, type or paste the access key ID of the user you want to find.
- If necessary, add the Access key ID column to the users table by completing the following steps:
- Above the table on the far right, choose the settings icon (
).
- In Manage columns, select Access key ID.
- Choose Close to return to the list of users and confirm that the filtered user owns the specified access key.
- Above the table on the far right, choose the settings icon (
Managing access keys (AWS CLI)
- To create an access key:
aws iam create-access-key - To deactivate or activate an access key:
aws iam update-access-key - To list a user’s access keys:
aws iam list-access-keys - To determine when an access key was most recently used:
aws iam get-access-key-last-used - To delete an access key:
aws iam delete-access-key
Managing access keys (AWS API)
- To create an access key:
CreateAccessKey - To deactivate or activate an access key:
UpdateAccessKey - To list a user’s access keys:
ListAccessKeys - To determine when an access key was most recently used:
GetAccessKeyLastUsed - To delete an access key:
DeleteAccessKey
Updating access keys
For details about granting IAM users permissions to update their own access keys, see AWS: Allows IAM users to manage their own password, access keys, and SSH public keys on the Security credentials page. You can also apply a password policy to your account to require that all of your IAM users periodically update their passwords and how often they must do so. For more information, see Setting an account password policy for IAM users.
Topics
- Updating IAM user access keys (console)
- Updating access keys (AWS CLI)
- Updating access keys (AWS API)
Updating IAM user access keys (console)
You can update access keys from the AWS Management Console.
To update access keys for an IAM user without interrupting your applications (console)
- While the first access key is still active, create a second access key.
- Sign in to the AWS Management Console and open the IAM console at https://console.aws.amazon.com/iam/.
- In the navigation pane, choose Users.
- Choose the name of the intended user, and then choose the Security credentials tab.
- In the Access keys section, choose Create access key. On the Access key best practices & alternatives page, choose Other, then choose Next.
- (Optional) Set a description tag value for the access key to add a tag key-value pair to this IAM user. This can help you identify and update access keys later. The tag key is set to the access key id. The tag value is set to the access key description that you specify. When you are finished, choose Create access key.
- On the Retrieve access keys page, choose either Show to reveal the value of your user’s secret access key, or Download .csv file. This is your only opportunity to save your secret access key. After you’ve saved your secret access key in a secure location, choose Done.
When you create an access key for your user, that key pair is active by default, and your user can use the pair right away. At this point, the user has two active access keys.
- Update all applications and tools to use the new access key.
- Determine whether the first access key is still in use by reviewing the Last used information for the oldest access key. One approach is to wait several days and then check the old access key for any use before proceeding.
- Even if the Last used information indicates that the old key has never been used, we recommend that you do not immediately delete the first access key. Instead, choose Actions and then choose Deactivate to deactivate the first access key.
- Use only the new access key to confirm that your applications are working. Any applications and tools that still use the original access key will stop working at this point because they no longer have access to AWS resources. If you find such an application or tool, you can reactivate the first access key. Then return to Step 3 and update this application to use the new key.
- After you wait some period of time to ensure that all applications and tools have been updated, you can delete the first access key:
- Sign in to the AWS Management Console and open the IAM console at https://console.aws.amazon.com/iam/.
- In the navigation pane, choose Users.
- Choose the name of the intended user, and then choose the Security credentials tab.
- In the Access keys section for the access key you want to delete, choose Actions, and then choose Delete. Follow the instructions in the dialog to first Deactivate and then confirm the deletion.
To determine which access keys need to be updated or deleted(console)
- Sign in to the AWS Management Console and open the IAM console at https://console.aws.amazon.com/iam/.
- In the navigation pane, choose Users.
- If necessary, add the Access key age column to the users table by completing the following steps:
- Above the table on the far right, choose the settings icon (
).
- In Manage columns, select Access key age.
- Choose Close to return to the list of users.
- Above the table on the far right, choose the settings icon (
- The Access key age column shows the number of days since the oldest active access key was created. You can use this information to find users with access keys that might need to be updated or deleted. The column displays None for users with no access key.
Updating access keys (AWS CLI)
You can update access keys from the AWS Command Line Interface.
To update access keys without interrupting your applications (AWS CLI)
- While the first access key is still active, create a second access key, which is active by default. Run the following command:
aws iam create-access-keyAt this point, the user has two active access keys.
- Update all applications and tools to use the new access key.
- Determine whether the first access key is still in use by using this command:
One approach is to wait several days and then check the old access key for any use before proceeding.
- Even if step Step 3 indicates no use of the old key, we recommend that you do not immediately delete the first access key. Instead, change the state of the first access key to
Inactiveusing this command: - Use only the new access key to confirm that your applications are working. Any applications and tools that still use the original access key will stop working at this point because they no longer have access to AWS resources. If you find such an application or tool, you can switch its state back to
Activeto reactivate the first access key. Then return to step Step 2 and update this application to use the new key. - After you wait some period of time to ensure that all applications and tools have been updated, you can delete the first access key with this command:
Updating access keys (AWS API)
You can update access keys using the AWS API.
To update access keys without interrupting your applications (AWS API)
- While the first access key is still active, create a second access key, which is active by default. Call the following operation:
CreateAccessKeyAt this point, the user has two active access keys.
- Update all applications and tools to use the new access key.
- Determine whether the first access key is still in use by calling this operation:
One approach is to wait several days and then check the old access key for any use before proceeding.
- Even if step Step 3 indicates no use of the old key, we recommend that you do not immediately delete the first access key. Instead, change the state of the first access key to
Inactivecalling this operation: - Use only the new access key to confirm that your applications are working. Any applications and tools that still use the original access key will stop working at this point because they no longer have access to AWS resources. If you find such an application or tool, you can switch its state back to
Activeto reactivate the first access key. Then return to step Step 2 and update this application to use the new key. - After you wait some period of time to ensure that all applications and tools have been updated, you can delete the first access key calling this operation:
Securing access keys
Anyone who has your access keys has the same level of access to your AWS resources that you do. Consequently, AWS goes to significant lengths to protect your access keys, and, in keeping with our shared-responsibility model, you should as well.
Expand the following sections for guidance to help you protect your access keys.
Note
Your organization may have different security requirements and policies than those described in this topic. The suggestions provided here are intended as general guidelines.